EU data protection
fromLondon Business News | Londonlovesbusiness.com
2 hours agoBritain's businesses hit by triple squeeze of costs and weak growth - London Business News | Londonlovesbusiness.com
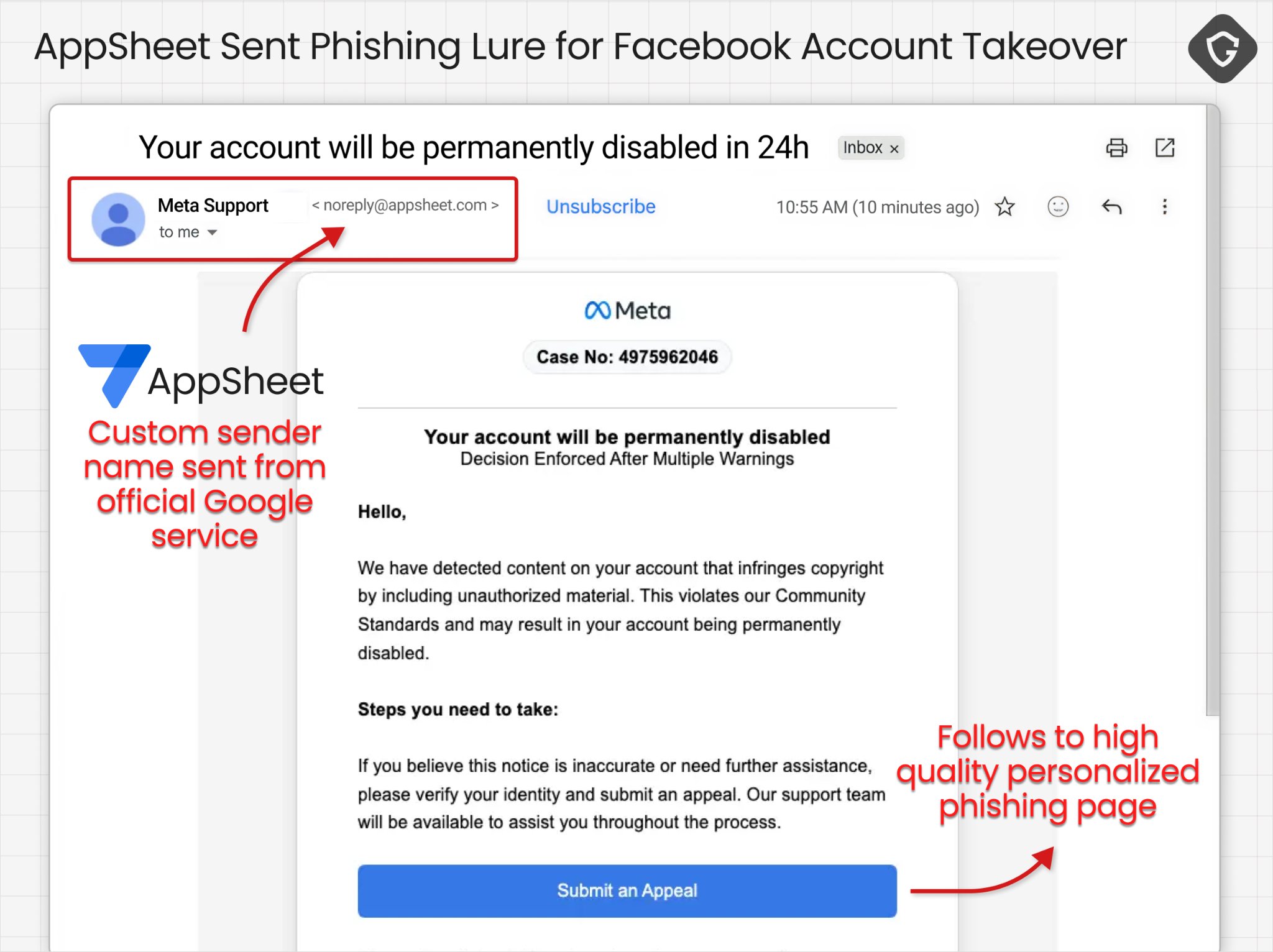
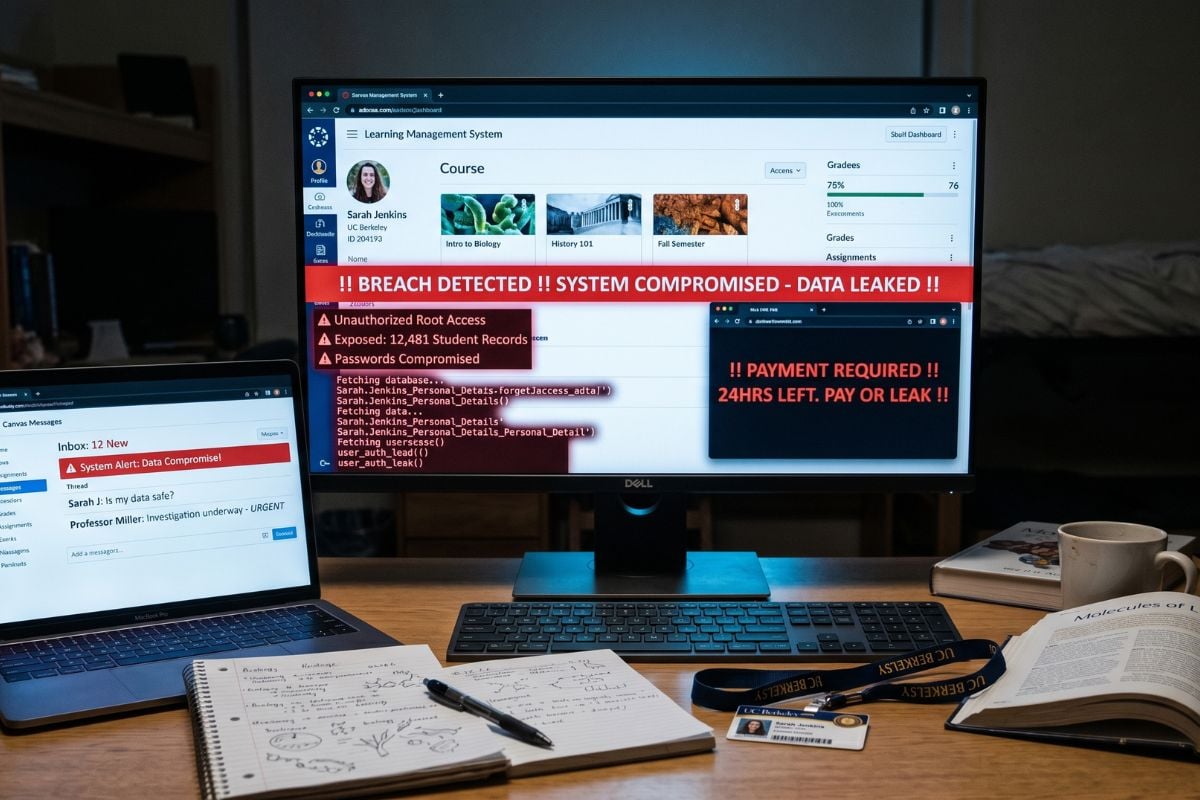
UK organisations face rising costs, weak growth, and cybersecurity threats, hindering AI adoption due to skills shortages and data protection concerns.








.jpg?height=635&t=1777921235&width=1200)
